Touch ID hackers attempt to take things to next level, no need for physical fingerprint



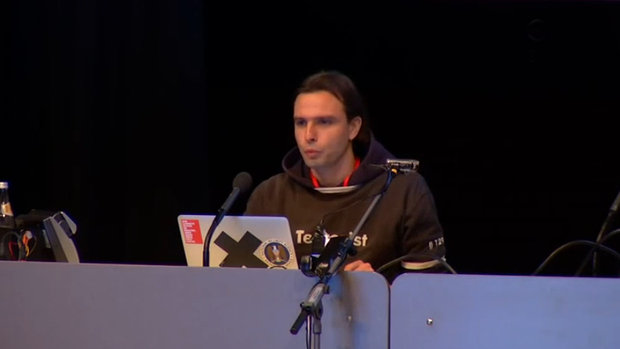
The hacker who successfully used a fingerprint captured from an iPhone to fool Touch ID now believes it may be possible to perform the same hack without needing access to a physical fingerprint.Speaking at this year’s Chaos Computer Club convention, Jan Krissler – who uses the alias Starbug – demonstrated how a fingerprint can be generated from a series of ordinary photographs of someone’s finger …

VentureBeat reports that he demonstrated the capability by photographing the thumb of German Defense Minister Ursula von der Leyen, using this to generate a fingerprint …
Krissler said he used commercially available software calledVeriFinger to pull off the feat. The main source was a close-up picture of von der Leyen’s thumb, obtained during a news conference in October, along with photographs taken from different angles to get an image of the complete fingerprint.
It’s worth noting that at this point, Krissler has not yet demonstrated an ability to combine the two approaches by using a photographed fingerprint to fool Touch ID, and that even if he is able to do so, the attack method is non-trivial. Last year’s video demonstrating the approach showed that it required 30 hours of work to pull off the first time, and would likely take several hours subsequently.
As we noted last time, the hack requires a considerable amount of time, effort, skill and equipment, and is not something the average iPhone user need be too concerned about.
Tests performed using the hack showed that while it still worked on the iPhone 6, Apple had improvedboth the security and reliability of the sensor in the new models.